My Thoughts: Passbolt Self Hosted Password Manager

For the past few years I have been playing about with the Passbolt password manager. This Open Source tool has been incredibly helpful for storing the hundreds of service account passwords that are used to manage all of the ayloNet infrastructure. I’ve noticed a number of significant improvements over the years, including the release of a suite of mobile-apps allowing the application to truly replace some of the big-name password managers. The following guide outlines how I’ve set up Passbolt and the process for onboarding new users.
The Setup
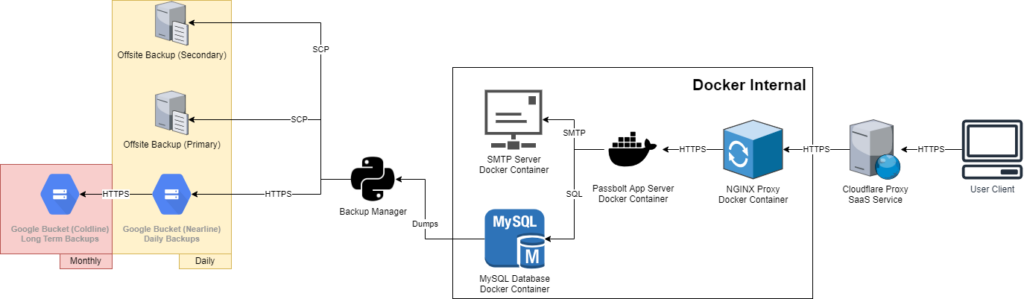
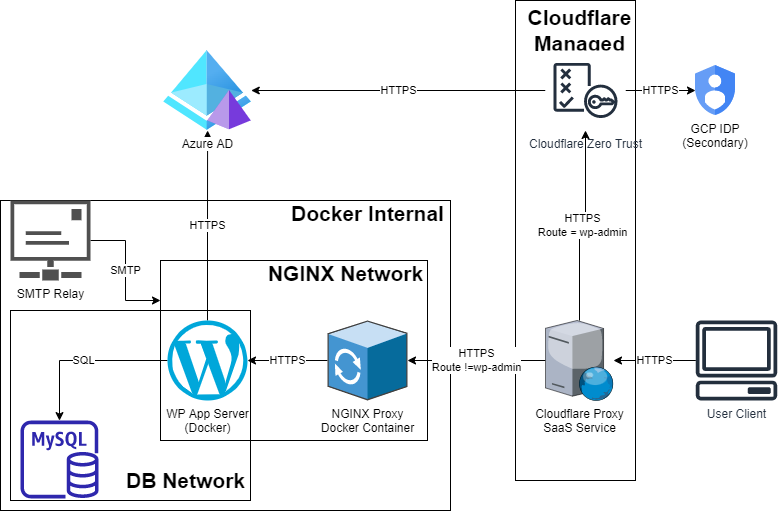
Figure 1 outlines the architecture of my Passbolt deployment which uses a range of Docker containers in order to deliver a secure and fast service to users. I have outlined the rationale and use of each component below:
- Cloudflare – Cloudflare’s proxy provides me with DDoS protection, improved cache and a faster load time for users by harnessing an industry leading CDN.
- NGINX Proxy – This proxy routes the incoming traffic (443) from Cloudflare to the correct service within the internal docker network. This is used so that none of the other containers need to be exposed directly to the internet. It also means that multiple containers can have external HTTPS access on the default port.
- Passbolt App Server – This should be obvious!
- MySQL Database – Stores all of the Passbolt data including the encrypted secrets, user details and group assignments.
- SMTP Server – Passbolt sends a number of emails to users, an SMTP server should be considered essential.
SSL is mandated throughout the entire architecture and non-https connections are blocked by default.
Full guidance for installing Passbolt can be found here. The installation is really simple and anybody with some prior Docker experience will be able to manage this deployment. I would STRONGLY recommend deploying a proxy in front of the app in order to ease the management of SSL certificates and allow improved container isolation.
User Experience
Put simply, the user experience is not as rich as many of the cloud hosted password managers. The majority of this comes down to the fact that Passbolt makes use of OpenPGP public/private certificate pairs to manage it’s encryption. The user is expected to retain a copy of the private key and if this is lost, the data is lost along with it. This does however ensure that Administrators can never access users’ passwords unless they have been specifically shared.
Passbolt has an app that is available on iOS and Android, allowing your users to access their passwords wherever they are. This app can be configured by going to settings and scanning a series of QR codes that appear on the screen. Biometiric authentication negates the need to re-enter the master password on each occasion. The Passbolt app is nice and simple, providing easy access to your vault while not faffing about with too many features that you don’t need!
Closing Thoughts
I really love Passbolt. It’s easy to deploy, maintain and use. It is well supported by it’s developers and there are constant feature enhancements even on the FOSS version that I use. While the setup is a tad complicated when onboarding a new user (and the need to protect the recovery kit is sometimes a tad stressful), its a very simple and effective password management tool with access across platforms. If you want to manage your own data or don’t trust one of the big providers, then definitely give Passbolt a go.
Just a reminder, please make sure the following are constantly backed up:
- Passbolt App Docker environment file.
- Passbolt Server Public Key (serverkey.asc)
- Passbolt Server Private Key (serverkey_private.asc)
- Passbolt database.
I’ve had a number of system failures, and completely migrated the app/db to a different server without any issues – but always remember to test your backups!
Edit: I’ve shared a really simple script below to help you backup your Passbolt Environment. Feel free to give it a go (as always, I take no liability if it doesn’t work